Securing your Applications in Node.js - Part 2/3
If you haven’t checked out the first part of Securing your Applications in Node.js, click here.
This is a 3-part blog series on Node.js. This article aims to establish a Node.js security roadmap by addressing security challenges comprehensively and consistently for large infrastructures.
- Part One: About Node.js, What does NodeSource do?, Understanding How Node.js Works, Understanding How N|Solid Works.
- Part Two: Security Principles & N|Solid Security
- Part Three: TIPS AND TRICKS on security in Node.js, Node.js Security in Architecture, Node.js Security in Development, Node.js Security in Deployment.
Let’s begin! 🚀
Security Principles
Talking about security can be a topic with a reasonably high scope, which is challenging because it has several edges to address it correctly. As a first approach to the concept, we want to present security with a basic definition:
*It is the degree to which a product or system protects information and data so that people or other products or systems have the degree of access to the appropriate data for their types and levels of authorization. *
Security is composed of differents subframes:
• Confidentiality, grade in which a product or system ensures that the data is only accessible to those authorized to have access. The best example is social networks.
• Integrity, the degree to which a system, product, or component prevents unauthorized access or modification of programs or computer data. Banking systems is a perfect example of this frame.
• Checking: You can evidence this step in digital signatures or audit logs. In checking, you demonstrated that actions or events took place so that events or actions can not be rejected later.
• Trace of responsibility, grade in which the actions of an entity can be traced uniquely to the entity. Specifically, this appears in security logs.
• Authenticity, a grade in which you can prove that the identity of a subject or resource is the claim, for example, in 2 factors authentication. Email, phone number. Biometric data.
These frames are not given in a specific order; however, in terms of security, it is essential to take this consecutive order into account in good practices.
The process gives this proposed order in terms of authentication, for example, on a website.
- User authenticates.
- Accesses a specific system module by registering the access time.
- The relationship between the movements and the objective of the transactions.
- If they are registered, the data of encryption or user access restriction is ensured that it is provided that the user is operating in data sections that comply with access restriction rules.
If you've ever wondered How we can improve Node.js security?
This is the checklist to apply to your node.js applications taking each of the states of your application: __Architecture, Development, and deployment. __
Before starting with tips and tricks to implement security in Node.js, we want to share that in NodeSource, we have a feature called Certified Modules - NCM that provides developers and software teams with actionable insights into the risk levels that are present in the use of third-party packages. If you want to learn more about avoiding npm substitution attacks using NCM, you can learn more in this Blogpost. We know for sure that it is the first step to understand security in Node.js. Run out a diagnosis that gives you a baseline to improve your application.
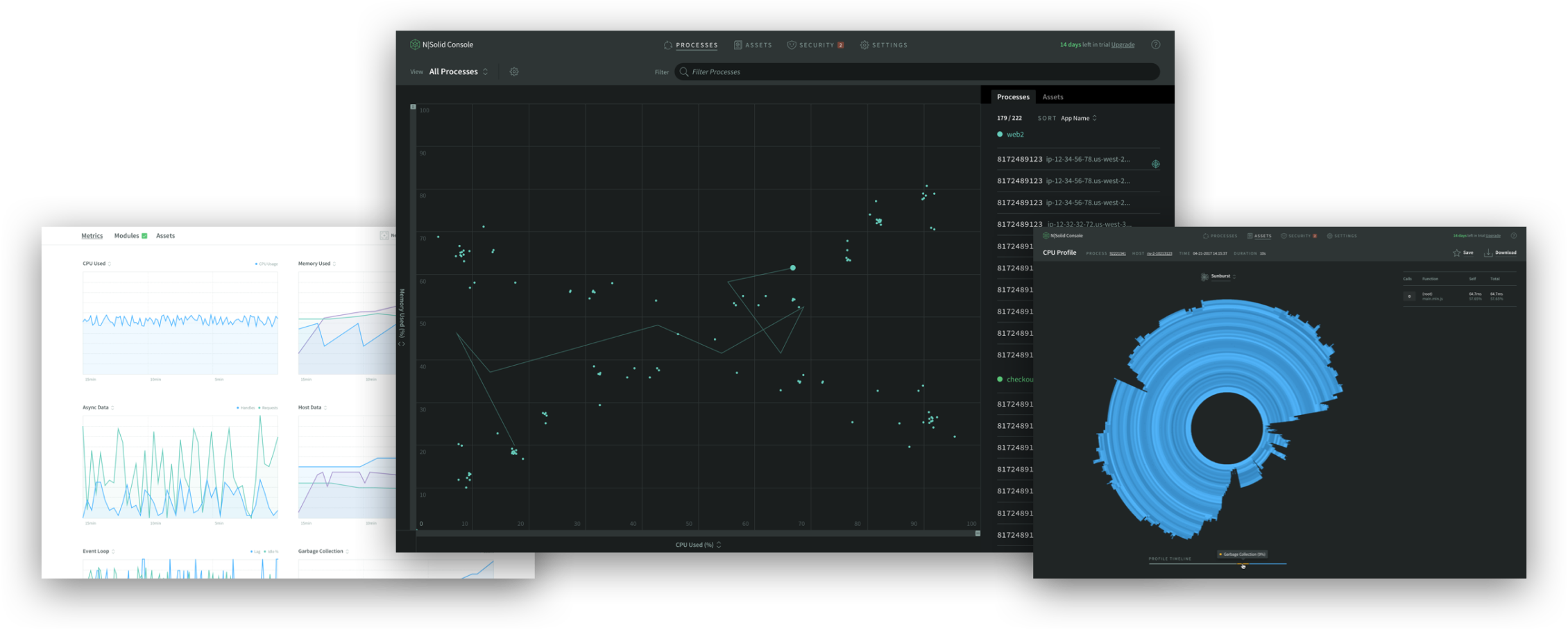
N|Solid Security

The safety of our star product, N|Solid, is the same safety of node.js. Our main task is to follow the patches that directly the core executes. We care about replicating them for up to 24 hours, thus always having our runtime in the latest version.
The best practices we follow are that our cluster is closed, our apps all compile private and publish everything in a private cluster. Only a port is exposed to interact with our resources; this is done following good container exposure practice at the containers and port level. Here is more about NCM in N|Solid Console and NCM Strict Mode.
Since our creation, our team has been clear about the implementation of good security practices; we invite you to review this content created by Dan Shaw @dshaw, one of our founders, and who has always opted for Node.js ✨ Achieving End-to-End Security with Node.js
In N|Solid, we have detection of vulnerabilities directly in the modules and several cool features that can improve the safety and performance of your applications; you can read more about our features at N|Solid.
Try N|Solid now!
If you have any questions, please feel free to contact us at info@nodesource.com or in this form To get the best out of Node.js, try N|Solid now! #KnowYourNode